Complete DNS Visibility for Your Organization
DNSCircle provides enterprise-grade analytics, real-time monitoring, and multi-framework compliance reporting – giving you full visibility into every DNS query across your network.
Real-Time Dashboard
Our live dashboard updates every 5 seconds via WebSocket, giving you instant visibility into network activity:
- Today’s Queries — total and blocked count at a glance
- 30-Day Threat Summary — threats blocked, allowed queries, unique blocked domains
- DNS Query Volume Trend — 30-day line chart showing total vs blocked queries
- Blocked Categories — doughnut chart breaking down blocks by category
- Hourly Activity Distribution — 24-hour bar chart revealing usage patterns over the last 7 days
- Block Rate Gauge — real-time percentage of queries being filtered
- Top Blocked Domains — sortable table with category and hit count
- Top Users — 7-day activity breakdown with per-user block rate
- Threat Intelligence Feed — recent detections with severity and threat type
- Live Query Stream — latest DNS queries updating in real time
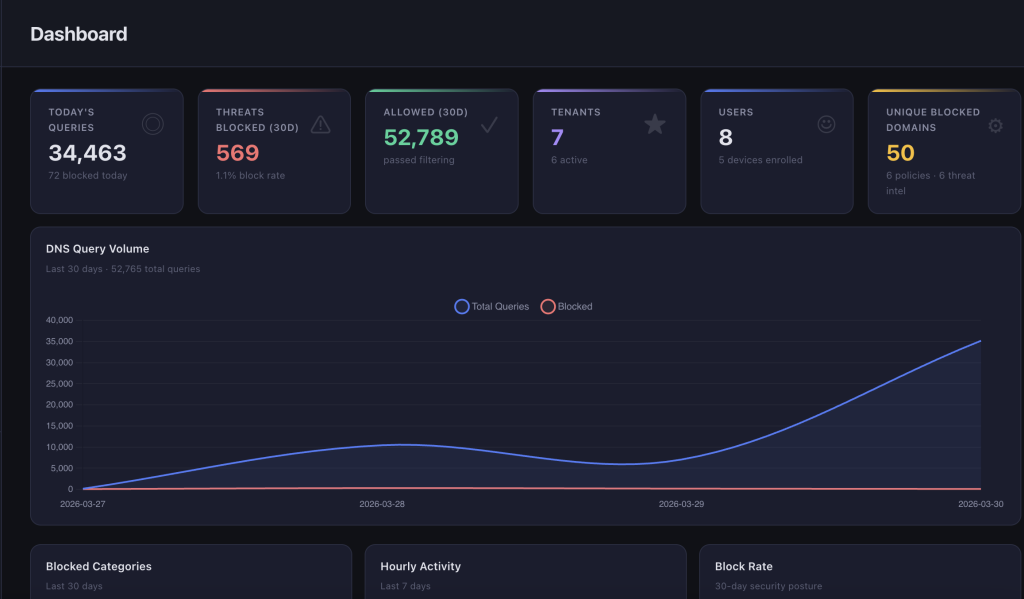
For MSP administrators, the dashboard aggregates metrics across all tenants with full data isolation.
Application Visibility
Understanding network traffic is no longer enough. Businesses also need visibility into which applications are being used, how heavily they are being accessed, and where security or productivity policies need to be applied.
With DNSCircle Application Distribution, organisations get a clear view of application usage across the network, from productivity platforms like Microsoft 365 and Google Workspace to communication, social media, and AI applications.

This helps teams:
• identify the most-used applications
• understand user behavior and query volume
• detect shadow IT and unmanaged app usage
• apply smarter security and access policies
• improve control without losing visibility
A modern DNS security platform should not just block threats. It should also provide meaningful insight into application usage so businesses can make informed security and productivity decisions.
DNSCircle brings together visibility, control, and DNS-layer protection in one intelligent platform.
Detailed DNS Query Logs
Every DNS query — allowed and blocked — is logged with full detail:
- Queried domain
- Filtering decision (allowed / blocked)
- Matched category
- User attribution (per-user DoH token tracking)
- Client IP address
- Query latency (ms)
- Timestamp with timezone support
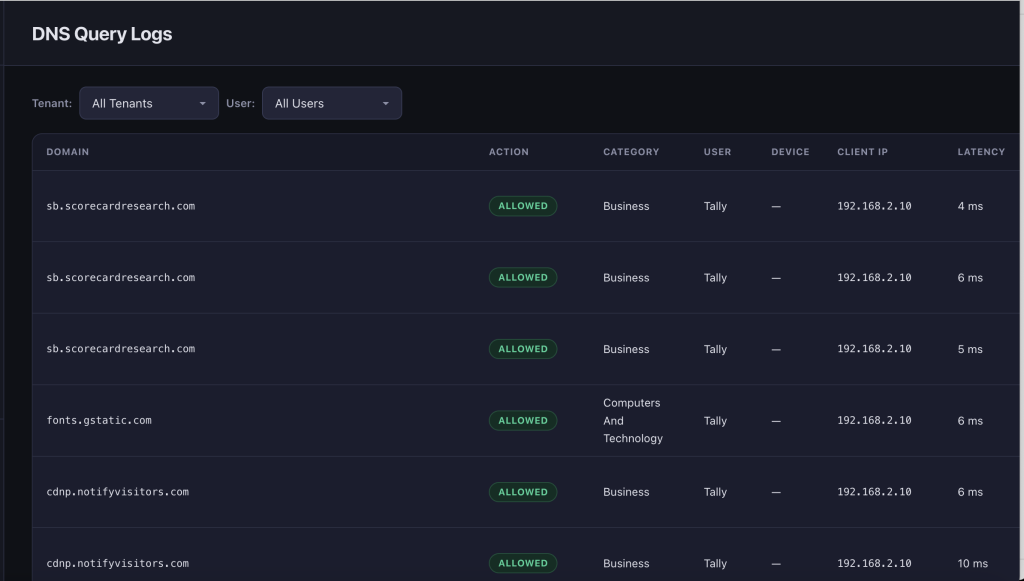
Logs are searchable, filterable by tenant and user, and invaluable for security audits and incident investigation.
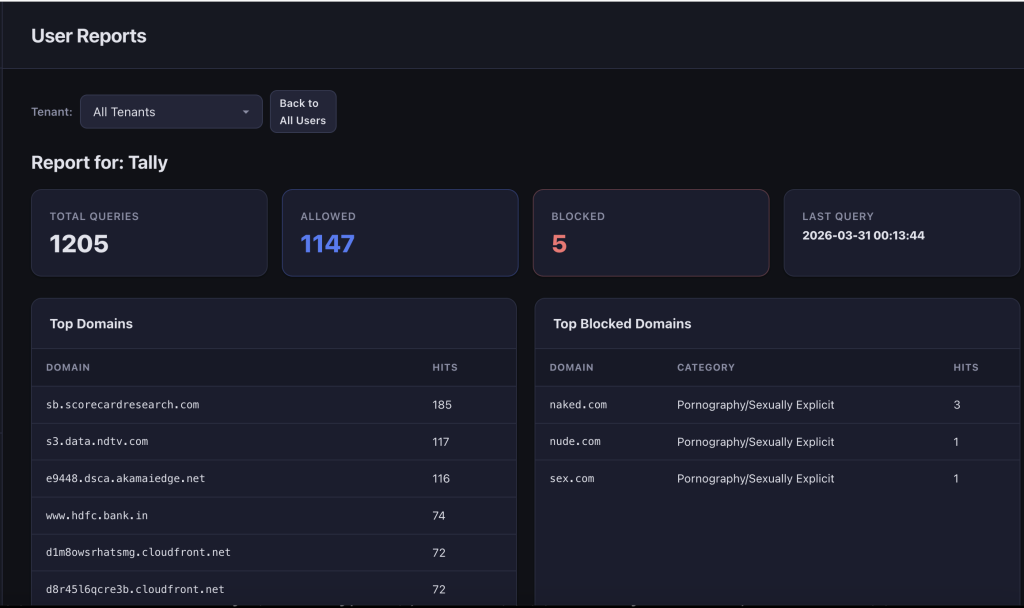
Per-User Reporting
Drill down into individual user activity to understand browsing behavior and policy effectiveness:
- Total queries, allowed and blocked per user
- Top domains queried with hit counts
- Top blocked domains with category labels
- Recent query history with full detail
- Last activity timestamp
Compliance Reporting — 5 Frameworks Built In
DNSCircle generates audit-ready compliance reports with customizable time periods (7 to 365 days) and CSV export. Each framework maps directly to your DNS filtering data:
HIPAA (Health Insurance Portability and Accountability Act)
Demonstrates ePHI protection with evidence mapped to Security Rule controls — 164.312(a) Access Control, 164.312(b) Audit Controls, 164.312(e) Transmission Security (DoH encryption), 164.308(a)(5) Security Awareness, and 164.312(d) Person Authentication.
SOC 2 (Service Organization Control 2)
Covers Trust Services Criteria — CC6 Security (logical access, threat management, transmission integrity), CC7 System Operations (monitoring, anomaly detection, incident response), and CC8 Change Management (policy controls).
PCI DSS (Payment Card Industry Data Security Standard)
Reports on Requirement 1 (network security controls), Requirement 4 (strong cryptography via DoH/TLS 1.2+), Requirement 5 (malware protection), Requirement 10 (logging and monitoring), Requirement 11 (security testing), and Requirement 12 (security policy enforcement).
CIPA (Children’s Internet Protection Act)
Content filtering metrics including categories filtered, filtering rate, users protected, and evidence of visual content filtering, internet safety policy, activity monitoring, and appropriate use education.
GDPR (General Data Protection Regulation)
Covers Article 32 (security of processing), Article 25 (data protection by design), Article 30 (records of processing), Article 33 (breach notification readiness), and Article 5(1)(f) (integrity and confidentiality)
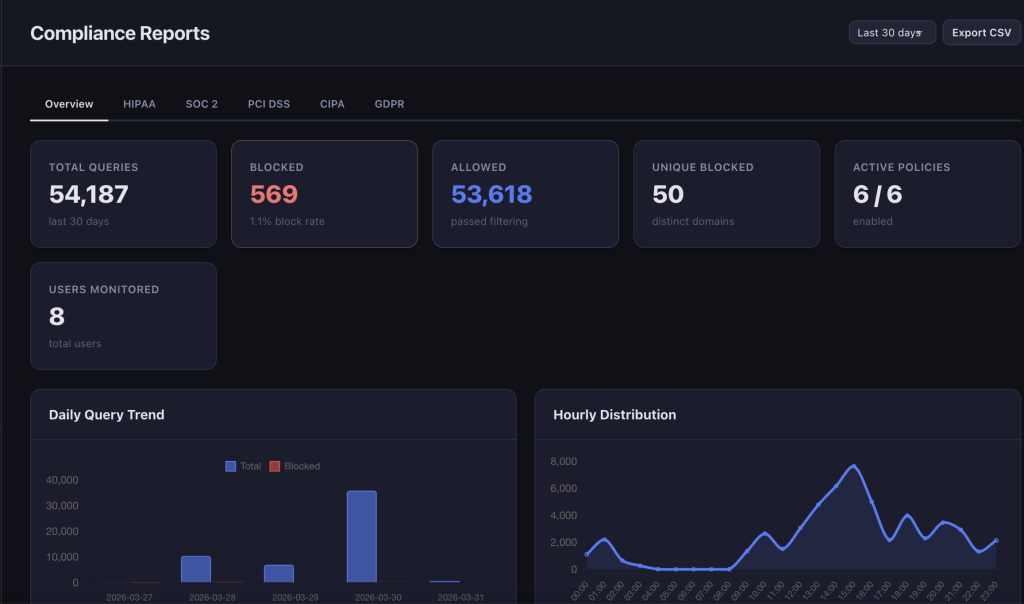
CSV Export
Export any report section as a timestamped CSV file for offline analysis or audit submission:
- Summary metrics
- Category-wise blocking statistics
- Domain-wise blocking statistics
- User activity logs
- Threat intelligence data
- Daily trend data
Threat Intelligence
DNSCircle automatically tracks and classifies threats as they are blocked:
- Domains are recorded with threat type (malware, phishing, C2, etc.) and severity level
- Hit counters track repeated access attempts
- Per-tenant threat category configuration
- Threat intelligence feed displayed on the dashboard with severity badges
Policy Analytics
Track how your filtering policies are performing:
- Per-policy hit counts updated in real time
- Active vs total policy metrics
- Policy coverage by scope — user, group, or global
- Category-level blocking statistics
Multi-Tenant Architecture
Every metric, log, and report is fully tenant-isolated:
- MSP Administrators see aggregated data across all tenants
- Tenant Administrators see only their own organization’s data
- Data isolation enforced at the query level across all analytics
Why It Matters
With precise, searchable data and real-time visual summaries, you can:
- Detect compromised devices early through anomaly patterns
- Understand user behavior with per-user drill-down
- Demonstrate compliance across HIPAA, SOC 2, PCI DSS, CIPA, and GDPR
- Proactively manage bandwidth and enforce acceptable use policies
- Export audit-ready evidence in seconds
